“Before you continue reading this post you need to be aware that the case study presents actual data and results from Google. We do not endorse using these kind of black hat practices. We only present them as they are being used and abused. Maybe Google will fix these faster. All for the sake of search transparency … “

High rankings for highly competitive keywords are still being obtainable, post “Penguin”, with black hat practices.
How do I dare to say that you might ask? Well because I have a case study that tells me so (plus I see them in the rankings day by day). It works the same way it worked 5 years ago. Well, Google did fix a few bugs here and there, but the black hat concepts are still the same and they still work.
Get a bunch of links and throw them at your target site.
Wait a minute. Don’t do it yet. Why? Well because here stuff starts to get different than it was 5 years ago. 5 years ago if you had a new domain and you would throw 1000 links at it, from 300 domains ( random example) your site would have been ranking in the top 5 for the following 2 weeks to a month , with a steady position … rarely you would have seen fluctuations.
Since then, Google has changed a lot. Some of the major changes that would stop such a black hat technique from working today are:
- The Google Index is being updated almost instantly (not weekly or daily)
- Google evaluates links with more in-depth knowledge of the link graph.
- Google takes in consideration Link velocity from a naturalness point of view.
- Google has human site reviewers that police the SERPs.
- and many more …
Let’s take our example and see how it still works today.
First we need to get our objectives straight:
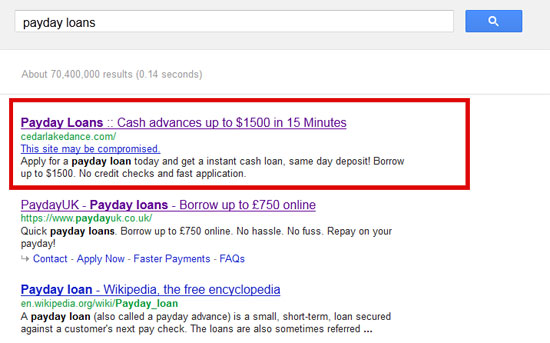
- One of the Top 3 positions on the keyword “payday loans” in Google (global) – this snapshot show us our site that was abused and ranked No.1 on this keyword.
Like with any cake you (your mommy, wife or girlfriend) cooks, you need to have some ingredients before you begin the actual cooking process. This is what it was used in our case:
Black Hat Ingredients
- One “aged”, well ranking site (you can choose any niche whatsoever – does not have to be related to the keyword you target) – cedarlakedance.com registered in August 2005
- A really good backlink analysis tool to check your competitors & identify how their link profile is constructed (by site type/link type/ link position/ metrics etc)
- A mix of high & low quality hacked sites where you will put links on.
- A Hacker.
- A cloacking script to detect Google Referrers.
- A Landing Page to convert visitors into Money.
These are the ingredients. Like with any other recipe … if you mix something wrong, the end result will be a failure (or an unexpected success 🙂 ).
Black Hat Directions
- Ask Hacker to check the site and find potential vulnerabilities. After this he will need to actually hack it and be able to put a html page on the server. (totally illegal – “DON’T TRY THIS AT HOME”)
- Don’t modify anything yet. Leave the site as it is.
- Use a top link analysis tool to analyze the top ranking sites (top 5) and get the number of referring domains they have.
- Analyze even more and classify by
- Dofollow /nofollow
- deep links /deep backlinks
- Profile backlinks by site type/ link type
- Profile backlinks by Authority Metrics
- After profiling their backlinks you will have a number of referring domains that you would target to achieve the No. 1-3 ranking. In our case the site settled to have approximately 600 referring domains in the end.
4. Apply the Google Bombing technique with a Link Velocity twist.
- Use the same anchor text (“payday loans”) everywhere. – no mix needed because of the Google trust that is applied to the victim site.
- Use the set of hacked sites to get your links live. This could be a private network of hacked sites or a set of link networks that would allow you to get blog posts or server side widgets posted.
- Important: All this needs to be done dispersed over a 1-2 week period of time ( in this case it was done starting with the approximative date of 14-May-2012 and it goes until 11-June-2012
5. Monitor the targeted keyword in Google until the victim site shows up (if you do not … watch the mix you did & retry)
6. Switch the original page with the Landing Page that you will use to convert the visitors into Money. Install the cloacking script also, so only people coming from Google will see the landing page and not anyone visiting the targeted page. Show Google the same page the Google visitors will see.
7. Monitor your targeted keyword. When you go down. Delete all the links that you have pointed to that target page so that you keep the link network secret to your competitors.
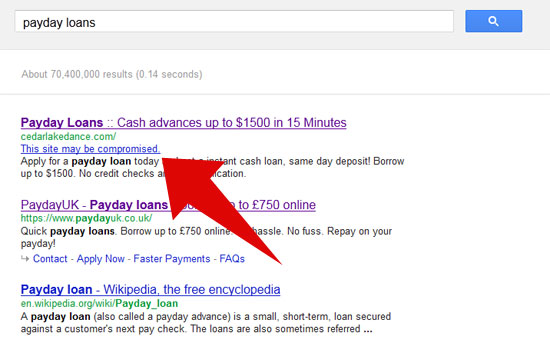
Ok. So let me exemplify with this site that got the No.1 ranking in Google … even after “Penguin” (sign that Google still has a lot of things to fix in their spam algorithm). First of all Google detects that the site might have been hacked. They do put a lot of effort in detecting this type of things. Google Alerts you about this in the SERPS.
Here is how the anchor text distribution profile looked before being abused.
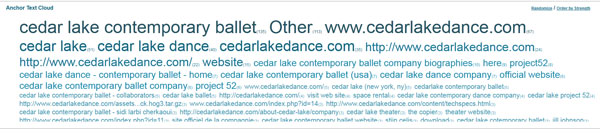
Here it is how it looks after being Google Bombed.

Here is the link velocity used to get the links on while Google Bombing the site.
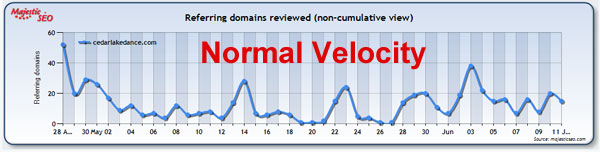
And here are the thinks that are unnatural … still Google things they are.
- ~ 40% of the link profile is made of abused new links over 2 weeks. Big proportion of different referring domain links acquired.
- Only “payday loans” anchor text was used.
- Only Dofollow Links.
- Only Text Links.
- The majority of links come from Russian sites ( totally unrelated to the previous link profile)
- All links point only to the main page of cedarlakedance.
In case you want to dig more into this, here is the CSV files to download with the entire link profile.
All this worked because the victim site was a trusted site, and Google considered this to be a spike in the sites authoritativeness. They did figured something out about the site being hacked, but they could not figure out the whole story. Until they do these kind of abuses will still work.
Practically these are techniques that are as old as the search engines are. The only thing that changes is just how these techniques are applied to make them work.
UPDATE
After a set of tweet exchanges with Ian @portentint & Ralph @fantomaster, I think it should be best noted that techniques that are using illegal practices (that are said to be illegal by the law) should be called “Crap Hat“ (evil search spam) and those that are only using SEO methods that are against the TOS of the particular search engine should be referred as “Black Hat”.
 Site Explorer
Site Explorer Keyword tool
Keyword tool Google Algorithm Changes
Google Algorithm Changes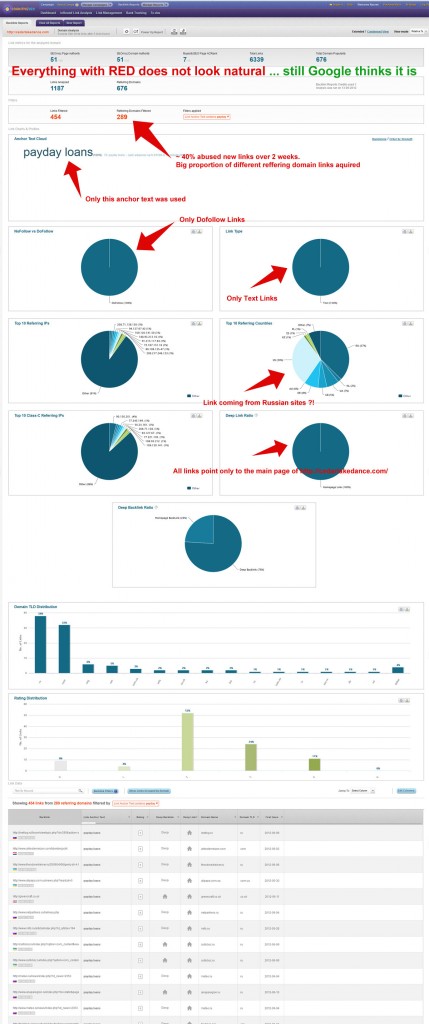


Great research. This is very common with WordPress sites but I have seen some folks who have tried this on Joomla using the admin password reminder exploit.
in their case is more complicated.the abused sites were not wordpress. the distribution varied pretty well.
I don’t watch Zone-h stuff anymore but those guys who exploit a entire server cluster can pull stuff like this off almost overnight.
Imagine if you had root access to a lousy web hosting company who provided shared/grid service.
Hackers are good people by the way, it is crackers who do naughty stuff like the ones highlighted above. 🙂
Wow. This is insane that even after everything going on recently, this sort of thing still works. Especially with quite a lot of media attention around topics like payday loans, you would’ve thought they’d pay more attention to trickery SERPs like these ones.
What would be a great test for this, is try it against a brand search, so “google” or “Wikipedia”/”bing” etc.
Think it would be a cool test to see the full extent of this and whether it would work against results that are likely to be monitored.
Great post!!
It’s shocking that black hat techniques like these are still having such a dramatic impact on search visibility post penguin. Clearly Google are still way off the pace with their ability to identify black hat practices!
This is brilliant. I feel bad for the cedar lake ballet team. What are some ways you can report hacked/stolen domains?
Interesting reading, goes to show that you’ll never completely stop a determined professional.
Hey Razvan,
So in summary, just hack a high PR/aged/Lots of BLs page then splash it with anchor text and mass link building to a landing page and watch it convert off the roof?
nope. the idea is that you need to have access to a large network of sites that you would control and interlink with the original site.
Great Research – the UK results are showing the same, with three of the top ten completely unrelated. What is really worrying is a SEO company is page one for “Payday Loans” – Advertising? I really hope not
https://www.google.co.uk/search?q=payday+loans&pws=0
I guess the question is how long did the ranking last for, how much traffic did it receive and did it provide a decent return on all the effort?
I saw it for at least 1 week there.
Cedarlake dance isn’t the only one I’ve seen with this same technique. 4 out of 10 are the same way for a non local search. Even more if you go deeper.
Two things that confuse me.
First – doing this sort of tactic when google is on an antispam crusade, for one of the notoriously spammy searches defies logic.
Second – to avoid detection the hack only redirects bots, not normal users. So the hack can’t harvest the bad seeds they’ve sown.
How can someone be that smart and dumb at the same time?
And who decides that the link is “unnatural” here?
well. if a trained human reviewer can do it … he will be used to train the AI algorithms to detect it too.
Thanks god I dont need a payday loan could get messy lol.
If some of You wonder is the juice worth the squeeze, just read this interview:
http://odigger.com/leadsmarket-co-founder-frank-kasimov-interview/
“How much do your highest earning affiliates make in a month?
One of our publishers makes about $200,000 a month.”
Hello,
I am truly shocked at how many people find this interesting. I really wasn’t aware of how many people didn’t know about Black hat SEO strategies, and the realm that they still work and “work very well”.
Things like this, do in fact make it hard on a White hat SEO. And for this reason, I ask that all of you go to Google and REPORT this type of TRASH MARKETERS, to Google and have them deindexed.
Just incase you also don’t know wheer to report spam to Google, I’m going to show you. Moreover, Matt Cutts recently posted a video, asking everyone to report junk sites and “idiot marketers” such as the one explained within the above article, to Google. Take a day and go through a few pages within Google performing link audits, and when you find a site that is obviously a BlackHat site, you can report them to Google by going here:
http://www.google.com/webmasters/tools/spamreport?hl=en
I am Gregory Smith os RxSEO.net and I really do appreciate you for taking the time to read through this comment, and the above article.
thank you!
I do not want to be a troll, but this -in nice words- is not a very logical idea. Google makes a huge amount of money through adwords search and search related data. If users have to do what google can’t do, then why should google profit from it? That should be totally google’s worry, not users. Or else they should not claim that they provide the best search results.
This is a great article, I will never ever try something like this but the time and effort that you put in here is admirable! I can see the practical application for getting your site to rank, still using link building strategies from way back although I would not recommend this if you do not know what you are doing!
Great Job!
Suspicions confirmed. I did a site colon and found the about page, which lead me to the social profiles. The company actively tweets and posts on facebook: cedarlakedance.com/about-cedar-lake
I called the phone number on their facebook and talked them through steps to clean this up.
we already talked on twitter, but for the rest.
the domain has been switched to anonymous domain registration back in Dec 2011. That might be a case of a hijacked domain and the owner might not have access to it anymore. The original content is usually kept so
all looks very accurate.
“A cloacking script to detect Google Referrers.”
This part is a bit inaccurate. It’s 2 lines oh php code that you put at the top of the infected page.
I think it’s a bit disingenuous to present that as a cloaking script at best.
I’m just curious as to what you think Google should do about this sort of thing?
They already deindex sites that REALLY ARE cloaking scripts. Would it be fair then to deindex the victims site? If not, what then is Google’s best course of action that they can handle algorithmically.
Remember, Google’s preferred course of action is based on algorithmic actions. It’s not as if there is a manual reviewer that looks at each and every “Real” cloaked site before it’s deindexed. One day it’s there, the next it’s gone.
Should that same algorithm then take out every .edu site that offers good/genuine content be deindexed if it’s been hacked? I’d love to see someone at Google explain that to the school’s board. (Not that they ever would.)
You make some good points and condemn the practice – but don’t finish the story with the conclusion on how to solve the problem.
From your point of view – how should the “Honest” search engine defeat the “Evil” blackhaters if deindexing isn’t enough already?
Cloacking scripts can be more advanced than that. They should contain list of ip address , times , refferes to which to cloack. What you refer to is very basic stuff.
In no way deindex the victim site … just identify that it is a malicious scheme and not rank it for the targeted keyword. If the site does not rank there than the interest is lost for the hack attempt. They already send Google Webmaster Tool messages to the site owner. (just need to have your email added there)
How to solve the problem?
By doing what they already do. Find unnatural link patterns better. And in this case it is kind of a straight way to be seen as it is only exact match anchor text bombed in a short period of time.
There is just too much trust in the original domain.
It should be balanced better in my point of view.
This stuff does work, I just don’t think it will stay very long. I give it 2 weeks to a month max.
Wonder how many sites are REALLY compromised like this? Doesn’t look like a lot with THIS query, but only Larry knows for sure: https://www.google.com/search?sugexp=chrome,mod=10&sourceid=chrome&ie=UTF-8&q=site%3Aspyfu.com+%22This+site+may+be+compromised.%22
that is very incomplete. you would need a complete cache of the google pages that saves that info.
Interesting study. This is way beyond anything I know how to do, but it’s good to know that people are able to cheat the system. I can only imagine the results on Bing if Google falls for this type of thing.
I think you mean “cloaking” not “clocking”.
I just cleaned up a hacked site today that was suffering from this. Show Google & other search engines pharma junk by adding links and changing titles, show everyone else the normal site. It was done via a single include in the index.php of WordPress.
sorry for the mistype. I corrected it.
Don’t fall for that persistent, insiduous Google propaganda which attempts to criminalize any SEO techniques they don’t like by lumping together “Blackhat SEO” with stuff that’s blatantly against the law in many jurisdictions such as hijacking websites, cracking password protected platforms and servers, botnets of hijacked zombie computers, malware & phishing links etc.
Yes, you really can use these actually illegal practices to achieve top rankings, but that’s what even Matt Cutts has been heard to refer to as “Craphat”. Blackhat SEOs may (and will) violate Google’s (and other engines’) Terms of Service (TOS), but they’re not into committing felonies, no matter how much Google may try to establish the perception that their TOS are the law of the land…
Else, I enjoyed the analysis part of the article – nothing new but a very nice case study.
Ralph,
The idea is exactly that it is old technique and it still works even after the “Penguin” update which addresses exactly these kind of issues. That was the main theme of the article.
Old good tricks never die … unless some big changes in the algo happen. Else they will still work.As we chatted on twitter at #SEMdays the BH needs to be even more paranoid.
Indeed – pointing out that it’s actually just another case of “new pile, same shit” (if you’ll pardon my French) is invaluable in terms of putting their “we just invented the wheel for a better user experience” hype into perspective is really invaluable.
And unless we fight their manipulative attempts at criminalizing SEOs with teeth and claws every inch of the way, we’re doomed to a fate much worse than having a few pages or sites deindexed…
Yes, you can’t ever be paranoid enough.
I can’t tell you enough how thankful I am that you posted this. So many SEO’s don’t play in this world but sometimes are left scratching their heads wondering how the hell site X is ranking well and getting away with it. I think all SEOs should read this and understand it. Getting blindsided by sites ranking well without knowing what is going on, or being able to explain why this is happening is tough, you’ve just made it a lot easier.
I am glad you found it useful.
The first think that any SEO should do when taking a new client or analyzing a new niche would be a similar backlink profiling like the one i did above.
It is quick and if you know at what to look you should get the main idea of the new niche in ~30 minutes.
Backlink Analysis will give you insights into what those guys are doing to be ranked there, and you could easily see how much(or not so much) work would be needed to get in the top 3.(if you can)
What’s bad here… is that the technique could be used both offensively and defensively. Don’t like someone’s ranking? Put them in a line of fire with penguin.
For anyone working in this vertical or other highly competitive verticals, this shouldn’t be a huge shocker. The SERPs for these types of queries have been a mess for weeks, and Panda/Penguin/etc haven’t corrected that. Between hacked sites, cloaked 301 redirects, and spam links, these guys continue to rank, and will do so until Google finds a way to *quickly* / automatically identify these tactics and devalue these sketchy tactics.
Firstly, Great post, thanks.
I don’t usually come out of the woodwork but this has been bothering me for some time.
I also see these SERPS on a daily basis and I and I’m pretty sure everyone who practices white hat SEO totally agree with you that some serious work needs to be done on Google behalf conserving the spam filter.
I have found that it is even more drastic than you have portrayed. I have noticed that there are sites that have absolutely zero metrics raking at the top of the SERPS and quite frankly have no idea why.
For example, in Google.co.uk there are 2 sites with lower than average metrics ranking for the term ‘Payday loans’ followed by 2 sites with zero metrics and zero links. Then there is an SEO company ranking and some compromised site. What is going on? Check it our for yourselves…
[URL=http://picturepush.com/public/8541984][IMG]http://www1.picturepush.com/photo/a/8541984/img/8541984.png[/IMG][/URL]
I wanted to write about these first but then decided on the No.1
It is tricky. They do have back links (either coming through redirects) / and checking the back links is very important with what tool you do it, either tool it needs to have the index update daily to be able to check this real time results.
Thanks Razvan!
I was only looking at the surface level through the SEOmoz toolbar. I know that after an in depth dig into these sites you will more than likely find some interesting information. Time to go digging! 🙂
Have a great weekend.
Wow! it is really unfair for honest seo marketers who are doing fairly with their seo techniques and not spamming or hacking a website just to rank on top of Google. Good thing that Google really did a good job of detecting this kind of techniques.. Good research Razvan
Google is still trying to work these things out. Anyway “salute” to them for the good work they done in the past years.
It is the job of the search engine to police its results. Competition is fierce in some fields …you just need to stay ahead of the curve. It’s like chess … strategy
Razvan, I tried to contact you on architect at cognitiveseo dot com but Remote host said: 550 5.1.1 … User unknown
😕
Is there any other way to get in contact with you?
Cheers!
I sent you a mail with the correct email address … why would i have architect @ can ?! 🙂
I am sharing this one , good job Razvan , top class analysis.